Secure video delivery: A decision framework for 2026

The media industry loses an estimated $75 billion annually to video piracy, with projections hitting $125 billion by 2028 (Kearney). That number gets quoted in every security pitch deck. What doesn't get quoted is how much of that loss comes from platforms that already had encryption, already had DRM, already had all seven security layers that every guide tells you to implement.
The problem isn't missing security features. It's applying the wrong layers to the wrong content. A free product demo and a $15/month premium series have completely different piracy economics, but most guides treat them identically: encrypt everything, DRM everything, watermark everything. The result is an overbuilt security stack that adds latency, burns engineering time, and protects content that nobody was going to steal anyway.
This is a decision framework for secure video delivery. Not a feature list. Not "here are 7 things, go implement all of them." Instead: which layers your content actually needs, based on what it's worth and who's watching it.
Most secure video content delivery guides list 7 security layers and imply you need all of them. You probably need 3. The minimum viable stack: encrypted delivery (HTTPS + HLS with AES-128), signed URLs with expiry, and JWT playback authentication. This covers roughly 90% of casual piracy scenarios. Add DRM, geo-blocking, forensic watermarking, and CDN-level protection only when content value, audience scale, or compliance requirements justify the added complexity.
Key takeaways:
A 2026 industry survey found that 73% of consumers are attracted to pirate sites for convenience, not because security was too weak to stop them (TVStrategies, 2026). They wanted everything in one place. Stronger encryption wouldn't have changed that.
Yet most teams building secure video delivery default to "stack everything." The thinking goes: if DRM is good, DRM plus forensic watermarking plus geo-blocking plus CDN token auth must be better. In practice, each additional layer adds measurable cost:
None of these costs are large in isolation. Stacked together on a free webinar that nobody is trying to pirate, they're pure waste. The question isn't "which security features exist" but "which ones earn their overhead for your content."
These three layers form the minimum viable security stack. They block direct downloads, prevent link sharing, and stop unauthorized playback. Almost every video platform needs all three, regardless of content value.
Layer 1: Encrypted delivery. HTTPS for transport encryption is table stakes. On top of that, HLS with AES-128 segment encryption ensures that intercepted video segments are unreadable without the decryption key. AES-256 is stronger but rarely necessary for streaming. The performance difference is negligible on modern hardware, but AES-128 has broader CDN cache compatibility.
Layer 2: Token-based access control. Every playback URL should be a signed URL with an expiration window. For VOD content, set expiry at 2-4 hours. For live streams, use per-session tokens that expire when the stream ends. A shared link that stops working after 3 hours is almost useless to a pirate. FastPix supports signed URLs for access control with configurable expiry, making this a single API parameter rather than a custom CDN configuration.
Layer 3: Playback authentication. JWT tokens verify that the viewer is authenticated before playback starts. Bind tokens to the user's session and device fingerprint so a copied token fails on a different device. FastPix uses JWT-based playback authentication with asymmetric key signing, which means the signing key never leaves your backend.
These three together handle the overwhelming majority of unauthorized access. Worth noting: this stack doesn't stop screen recording. Nothing does. If that's your primary threat vector, you need deterrence (watermarking), not prevention.
The remaining four layers: DRM, geo-blocking, forensic watermarking, and CDN-level protection. Each one has a specific trigger. If the trigger doesn't apply to your content, skip the layer.
Layer 4: DRM. Add DRM when your content has resale value on pirate markets. A $15/month subscription with exclusive content qualifies. A free product tour doesn't. DRM enforces licensing rules at the device level: Widevine L1 for hardware-backed protection on Android/Chrome (covers roughly 85% of those devices), FairPlay for iOS/Safari, PlayReady for Windows/Edge. FastPix provides DRM-ready streaming outputs without requiring separate packaging services. The tradeoff: 200-800ms added to initial playback for license acquisition.
Layer 5: Geo-blocking. Required only when content carries regional licensing restrictions. If you've licensed a film catalog for the US market only, geo-blocking isn't optional. Combine IP-based restrictions with VPN detection (commercial services catch 80-90% of known VPN ranges) and impossible-travel detection. If your content is globally licensed, skip this entirely.
Layer 6: Forensic watermarking. Add this when a single leak costs more than the watermarking infrastructure. For a platform serving 50,000+ concurrent viewers on premium content, forensic watermarking lets you trace leaks to the specific viewer session. Forensic watermarks survive re-encoding, cropping, and compression. For platforms under 5,000 viewers, visible watermarking (user email overlay) provides most of the deterrence value at a fraction of the cost.
Layer 7: CDN-level protection. This covers hotlink prevention, DDoS mitigation, and origin shielding. Hotlink prevention blocks other sites from embedding your video URLs directly, a common bandwidth-theft tactic covered in detail in the CDN leeching and stream protection guide. If your streams are publicly embeddable by design, some CDN protections don't apply. If you're serving premium content on your own player only, enable referrer validation and signed CDN tokens.
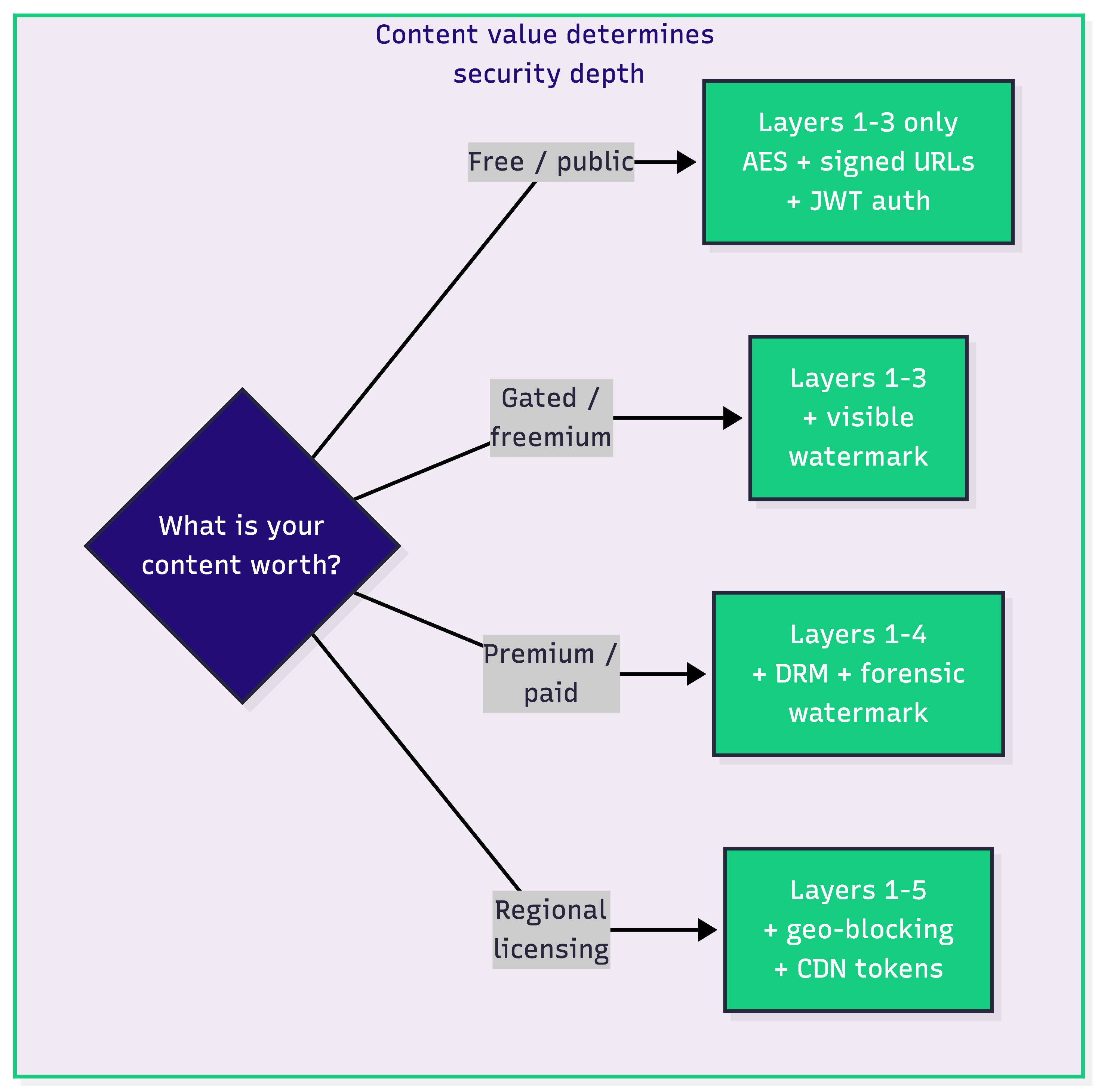
Not every platform faces the same threats. An OTT service with exclusive originals has a completely different piracy profile than an enterprise training portal behind SSO. This table maps required layers by vertical, including content with regional licensing and rights restrictions.
Regional rights content (the rightmost column) requires the heaviest stack. If you've licensed content by territory, geo-blocking plus DRM plus signed URLs are all mandatory. This is the one scenario where "stack everything" is the correct answer, because a single geo-leaking incident can trigger contract violations.
You can test the full signed URL and DRM-ready pipeline with $25 in free credits to see how these layers work together before committing to a full implementation.
Each of these layers has a dedicated deep-dive guide in the FastPix security content library. This section gives the implementation threshold and links to the full walkthrough.
Encrypted delivery: Enable HTTPS on your CDN (non-negotiable in 2026) and configure HLS with AES-128 segment encryption. Key rotation: every 24 hours for live streams, per-asset for VOD libraries. More detail in the CDN leeching and stream protection guide.
Signed URLs: Generate URLs server-side with a cryptographic token and timestamp. Set expiry between 2 and 6 hours for VOD, per-session for live. Full implementation walkthrough in how to protect video content with signed URLs.
JWT playback auth: Issue short-lived JWT tokens (15-30 minute expiry) from your authentication backend. Bind to session ID and device fingerprint. FastPix supports JWT-based playback authentication with asymmetric key signing and automatic token rotation.
DRM: Use DASH with CENC (Common Encryption) for a single encrypted file compatible with Widevine, FairPlay, and PlayReady. Detailed in DRM explained and the DRM and content protection guide.
Geo-blocking: Enforce at the CDN edge, not in your application layer. Combine with VPN detection and behavioral signals. Pair with DRM for content with territorial licensing.
Forensic watermarking: Choose between visible watermarking (email overlay, near-zero cost) and forensic watermarking (pixel-level, survives re-encoding). See forensic watermarking guide and watermarking vs. fingerprinting.
CDN protection: Enable referrer validation, signed CDN tokens, and DDoS mitigation. Block hotlinking by restricting playback to your domain. Covered in the CDN leeching and stream protection guide.
Security isn't about how many layers you stack. It's about matching layers to what your content is actually worth. Three layers cover most platforms. Seven layers are for premium content with regional licensing, high piracy risk, and compliance requirements. Everything in between is a decision, not a default.
Start with the 3-layer minimum and scale up as your content value grows. Get $25 in free credits to test the full secure video delivery pipeline.
Encryption key management directly determines whether video security holds or breaks. For live streams, rotate keys every 24 hours minimum to limit the window of exposure if a key leaks. For VOD, generate per-asset keys so a compromised key doesn't unlock your entire library. Store keys in a dedicated key management service, never in client-side code. Deliver decryption keys over HTTPS with token validation, and ensure compromised keys can be revoked within minutes.
Multi-DRM requires three separate integrations with different license server protocols. Widevine covers roughly 85% of Android devices and Chrome browsers. FairPlay handles iOS and Safari. PlayReady covers Windows and Edge. The practical challenge is maintaining a single encrypted file using CENC (Common Encryption) while managing three license delivery paths. Each DRM adds 200-800ms to initial playback for license acquisition, and debugging DRM failures across devices is time-intensive because error messages are intentionally vague for security reasons.
Commercial VPN detection services block 80-90% of known VPN IP ranges, but residential proxies bypass detection at a 30-40% rate because they route through real ISP addresses. Effective geo-blocking layers multiple signals: IP reputation databases, impossible-travel detection (streaming from Tokyo and London in the same hour), and device fingerprinting. No single method is foolproof. For content with territorial licensing obligations, pair geo-blocking with DRM and signed URLs so circumventing one layer doesn't expose the content.
Three layers cover roughly 90% of casual piracy scenarios. First, encrypted delivery using HTTPS plus HLS with AES-128 segment encryption. Second, signed URLs with 2-4 hour expiry for VOD and per-session tokens for live streams. Third, JWT playback authentication with session binding and device fingerprinting. This stack blocks direct downloads, kills shared links after expiry, and prevents unauthorized playback on unregistered devices. Add DRM, geo-blocking, and forensic watermarking only when content value or compliance requirements justify the added latency and infrastructure cost.
AES-128 encrypts HLS video segments, but the decryption key URL is visible in the playlist file. Any HTTP client can grab the key and decrypt the content. DRM uses a license server and hardware-backed Content Decryption Module (CDM) to manage keys in a protected environment that browser dev tools cannot access. Widevine L1 provides hardware-level key protection on supported devices, while L3 offers software-only protection with weaker guarantees. DRM also enforces output protection rules like HDCP to prevent capture from display outputs, something AES encryption alone cannot do.
