How to protect online courses from piracy

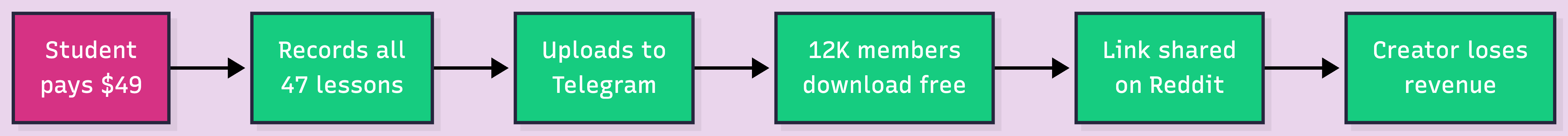
Three days after launching a $299 advanced Python course, an EdTech startup's lead instructor sent a Slack message to the engineering team: "My entire course is on Telegram. All 47 videos. Free." The platform had a "DRM Protected" badge on every video page. The marketing site promised enterprise-grade security. None of it mattered.
The leak wasn't a DRM bypass or a key extraction exploit. A paying student had screen-recorded every lesson with OBS Studio, uploaded the files to a Telegram channel, and shared the link on Reddit. The "enterprise-grade" DRM did exactly what DRM does: it prevented direct downloads. It did nothing about someone hitting record.
The content protection market hit $18.5 billion in 2026 (MarketResearchUpdate.com), and most of that spending goes to DRM. But course piracy doesn't work the way OTT piracy does. Your threat model is different, and the strategies that actually work are different too.
Course piracy is different from streaming piracy. Courses are finite (47 videos, not an infinite catalog), shared through Telegram groups and browser extensions, and often pirated by the students themselves. Access control (signed URLs, JWT tokens, session limits) blocks most leaks at near-zero cost. DRM adds value at scale but cannot stop screen recording. Non-technical strategies like community access, live components, and regional pricing are often more effective for EdTech than encryption.
Key takeaways:
Course piracy is slower and more personal than OTT piracy. The most common vector isn't a sophisticated exploit. It's a student who paid $49, screen-recorded 47 videos over a weekend, and uploaded a zip file to a Telegram group with 12,000 members. That link hits Reddit, gets 200 upvotes, and now your entire course is free.
On March 25, 2026, the US Supreme Court ruled that ISPs are generally not liable for their users' copyright infringement (Los Angeles Times). The burden of protecting course content now sits entirely on the platform builder.
The critical difference: courses are finite assets. A course has 47 videos. A pirate can methodically record every one over a week. That changes the math.
This is where the real work happens. If you've read our OTT piracy prevention blog, you know the conceptual framework. This section goes deeper on the access control implementation that article references.
Every playback request should go through a signed URL. Your backend generates a URL with a cryptographic token and expiration timestamp. The CDN validates both before serving any video segment. Shared, copied, or expired URL? Playback fails.
For course platforms, set expiry between 2 and 6 hours. Shorter than a study session causes frustration. Longer than a day gives students time to share working links.
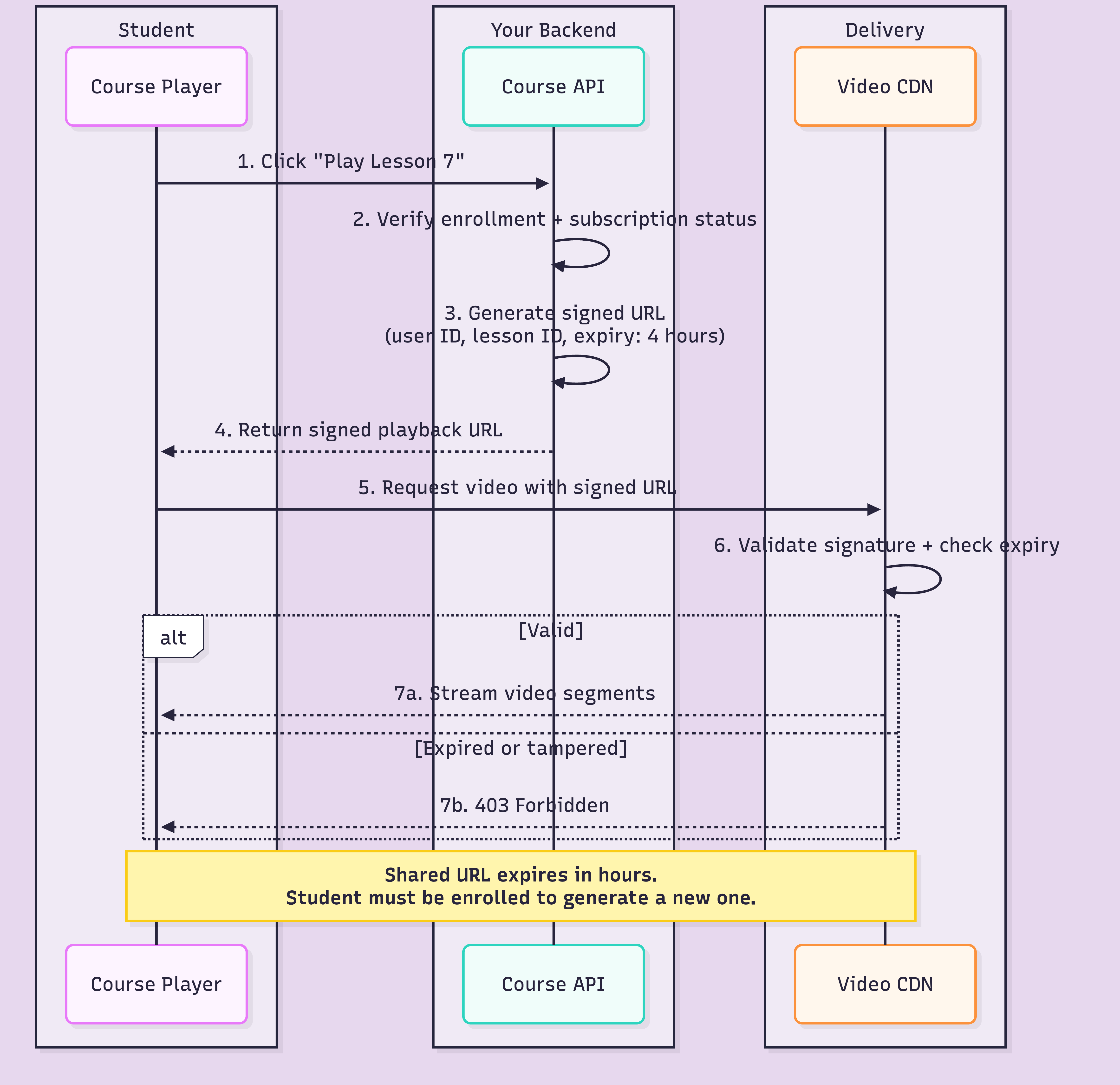
Signed URLs handle link sharing. JWT tokens handle credential sharing. Your backend issues a short-lived JWT (5-minute expiry) that encodes the user's session, device fingerprint, and playback permissions. The CDN validates both the signed URL and the JWT before serving content. Two independent checks, two independent expiry clocks.
One account, two or three concurrent streams max. Fourth device starts? Oldest session terminates. This is the single most effective measure against credential sharing for courses.
Why it matters more for courses than OTT: a shared Netflix account still generates value because each person watches different content. A course account shared between 20 people means 19 people who should have paid didn't. Set the limit at 2 concurrent sessions and force re-authentication on new devices.
If one account hits playback endpoints from 15 different IPs in an hour, that's not a traveling student. Flag accounts with unusual IP diversity for manual review. Don't auto-ban (mobile networks switch IPs), but surface anomalies to your moderation team.
At FastPix, access control is handled through the API: signed URL generation, JWT-based playback authentication with token rotation, and asymmetric key signing. You can try the full signed URL and token flow yourself with $25 in free credits.
The decision comes down to a simple calculation: course price times student count equals how much you stand to lose.
This trips up more EdTech teams than anything else. HLS supports AES-128 encryption. The video segments are encrypted. The manifest references a key. Feels secure.
The problem: the key URL sits right there in the playlist file. Any HTTP client can fetch the key, download the segments, and decrypt them locally. AES-128 stops right-click saving. It does not stop anyone with browser dev tools.
For courses under $100 with fewer than 1,000 students, AES-128 plus signed URLs is reasonable. But if your course costs $500 and you have 50,000 students, you need actual DRM.
Full DRM means three systems: Widevine (Chrome/Android), FairPlay (Safari/iOS), PlayReady (Edge/Windows). Most video APIs handle multi-DRM packaging automatically using Common Encryption (CENC). FastPix provides DRM-ready streaming outputs for all three without separate pipelines.
For the deep dive on how DRM works, Widevine L1 vs L3, and why the analog hole makes DRM insufficient alone, see our OTT piracy prevention guide.
These strategies are unique to education. No OTT piracy guide covers them because they don't apply to streaming. For courses, they're often more effective than encryption.
A pirated course gives you 47 video files. The legitimate version gives you weekly Q&A with the instructor, a Slack channel with 2,000 students, accountability partners, and industry networking. You can't pirate a community.
The video files become the entry point, not the product. Pirating videos without the community is like stealing a gym's workout plan without access to the equipment.
Release 3-4 videos per week instead of unlocking all 47 on day one. Cohort-based delivery means students progress together, with discussions tied to the current week's content. A pirate who grabs Week 1 still can't access Week 8.
This also improves completion rates. Most courses have completion rates below 15%. Drip content with cohort accountability pushes that number significantly higher.
Live Q&A sessions, office hours, workshops, code reviews. These happen in real time and can't be replicated from a zip file. The more live interaction you build in, the less the video files alone are worth to a pirate.
If your course issues certificates that employers recognise, pirated videos don't come with them. Link issuance to platform-verified completion: quizzes passed, assignments submitted, watch time tracked through player analytics.
Legitimate streaming availability decreases piracy by 15% to 20% (Initiative for Digital Entertainment Analytics). A student in India pirating a $299 course might happily pay $29 with purchasing power parity pricing. Regional pricing removes the strongest motivation for price-driven pirates.
Screen recording exists. At some point, DRM will fail. You need a way to trace leaks back to the source and deter casual sharing before it starts.
Forensic watermarking embeds an invisible, unique identifier into each student's video stream. When a leaked copy surfaces, you extract the watermark and trace it to the exact account that captured it. This is the gold standard for leak attribution at enterprise scale.
TagMango, a creator monetization platform serving thousands of online educators, takes a deterrence-first approach to content protection. Their system combines DRM encryption with visible watermarking: each student's email address is overlaid on the video during playback, making any screen recording traceable to the account that captured it.
This is not forensic watermarking. A visible overlay can be cropped or obscured before sharing. But for the creator economy, deterrence often matters more than enforcement. Most students sharing course content are not running sophisticated removal tools. They are screen-recording and uploading to Telegram. A visible email overlay on every frame makes that a risk most casual pirates will not take.
Only about 9% of takedown requests succeed (Verimatrix, 2026). But for course creators, specific actions improve the odds:
Automated monitoring at volume is the only way to make takedowns work at scale. Manual notices are whack-a-mole.
For leak tracing, you'll need a dedicated watermarking service. FastPix handles access control and DRM: signed URLs, JWT playback authentication, and DRM-ready outputs through a single API.
If your signed URLs don't expire and your sessions aren't bound, you're paying for encryption while leaving the front door open.
Start at the top. Get access control working. Layer DRM when revenue justifies it. At every stage, invest in non-technical strategies that make your product worth more than a zip file.
If you're building a course platform and want access control and DRM without stitching together five services, that's what we built FastPix for. The API reference walks through signed URL generation and playback token setup.
Get $25 in free credits and test the full access control pipeline. Try now!
AES-128 encryption protects HLS video segments with a symmetric key, but the key URL sits in the playlist file where any HTTP client can grab it. Full DRM (Widevine, FairPlay, PlayReady) uses a license server and hardware-backed Content Decryption Module to manage keys in a protected environment. AES-128 stops right-click downloads. DRM stops technically skilled users. For courses under $100 with fewer than 1,000 students, AES-128 plus signed URLs is usually enough.
Not if you implement signed URLs with short expiry windows. A signed URL includes a cryptographic token and timestamp that the CDN validates before serving video segments. When the token expires (typically 2-6 hours), the URL stops working. Pair this with session binding, where the playback token is tied to a specific authenticated session, and shared links fail authentication entirely.
Yes. Community access creates value that video files alone cannot replicate. A pirated course gives you 47 video files. The legitimate course gives you instructor Q&A, peer discussions, networking, accountability partners, and often live sessions. Platforms that bundle community features with course content report lower piracy-driven churn because the product extends beyond downloadable media.
Start with forensic watermarking to identify the leak source. For Telegram, file DMCA takedowns through telegram.org/dmca. Automated monitoring services can scan Telegram channels continuously. The most effective approach combines watermarking (to trace leaks), monitoring (to detect them fast), and DMCA (to remove them). Only about 9% of takedown requests succeed (Verimatrix, 2026), so prevention through access control matters more than removal.
No. DRM prevents downloading and redistribution of the original encrypted file, but it cannot stop screen recording. This is the analog hole, and every DRM system has it. Forensic watermarking is the only technical measure that makes screen-recorded leaks traceable to the specific user who captured them.
Start with access control: signed URLs with expiry and concurrent session limits (max 2-3 devices per account). This blocks link sharing and casual credential sharing at near-zero cost. Add visible watermarking with the student's email as a deterrent. Skip DRM until you have more than 1,000 students or your course costs more than $200. Focus energy on building community and live components that pirates cannot replicate.
